Choosing the Right ERP SOftware For Small Businesses
Effective operations management is essential for small manufacturing businesses in today’s fast-paced business environment.
Read MoreIPMC GHANA
Best Cyber Security Certifications to Boost Your Career
TIn digital environment cybersecurity companies are providing many best cybersecurity services in the world.
Read MoreIPMC GHANA

Te Latest Trends in ERP Software
Keeping up with trends is crucial in the fast-paced business world. It is particularly relevant to small businesses, which place a premium on efficiency and adaptability.
Read More IPMC GHANA
Types of Software Maintainance: A Comprehensive Guide
Software maintenance is the process of updating and changing the client’s software system. This includes updating the software to work with new upgrades....
Read MoreIPMC GHANA

The Role of SD-WAN in Optimizing Cloud Network
SD-WAN serves a significant role in optimizing cloud networks by providing improved flexibility, performance, and control over network traffic. Also, the organizations that...
Read MoreIPMC GHANA

Types of Cyber Threats: Understanding Online Vulnerabilities
Life has become more comfortable with various digital devices and the internet that makes them possible. Everything has a downside. The contemporary digital world is...
Read More IPMC GHANA
AI Revolution in CyberSecurity
AI Revolution has transformed the way businesses operate. The way we protect digital assets is changing as a result of the potential AI holds, which is tapped by an array ........
Read MoreIPMC GHANA

Trend Setting in Africa With IPMC
TrendsNAfrica recently interviewed our CEO Mr Amar Deep Singh Hari and they talked about his entrepreneurial journey and the role that Indian diaspora has played in shaping........
Read MoreIPMC GHANA

Top 10 CyberSecurity Tips for Holiday Shopping
Consumers are longing for normalcy, waiting for something to celebrate, planning to spend money during the holidays—but differently from the way they have in the past ....
Read More IPMC GHANA
These 5 Types of Hackers Are A Threat to SMBS
These 5 types of hackers are a threat to SMBs Malicious hackers are motivated by different things. Some want money, some do it for fun while others just want to end your .......
Read MoreIPMC GHANA

Delievering Hope to India at a Time of Need
Ghana’s collective effort to help a friend in whatever capacity possible, is symbolic of courage & not accepting defeat at the hands of circumstance .......
Read MoreIPMC GHANA

The Importance of Collaborations in IT
One organisation alone cannot achieve all innovation and create advantages for all sectors they serve. When technologies are combined, ........
Read More IPMC GHANA
Is the Riot Worth it to Spend On ERP Softwares ?
An ERP project is not a small investment for a business. Starting with licensing and going up to post implementation maintenance, the costs are significant enough to ........
Read MoreIPMC GHANA

Cyber Security in the Times of Covid-19: How to Avoid These Top Security Mistakes and Secure Your Business ?
As more and more businesses go digital, the number of users increases, and the amount of data from personal records, to financial records, to critical business processes ........
Read MoreIPMC GHANA

Top Trends in Tech in 2021
What are the latest tech developments that you think will be the next big thing?
Read More IPMC GHANA
IPMC Journey to Become West Africa's IT Leader
Recently, Forbes Africa did a feature on IPMC Ghana as a part of their special coverage of West Africa’s rising stars. While it is an honour to be featured in a publication ........
Read MoreIPMC GHANA
Together let's Fight Childhood Cancer
At IPMC Ghana we believe that Children are the future of our country and it is our utmost responsibility to take care of them. As part of our CSR initiative, ........
Read MoreIPMC GHANA

Here is How AI and ML Enhance Your Career Prospects
Almost every aspect of life in the coming decades will involve AI to some extent. From customer service to logistics and transportation, even medicine could get an ........
Read More IPMC GHANA
Is Your Enterprise Protected From Cyberattacks ?
Last year was full of uncertainties. Businesses had to brace up to survive. They had to shift and adapt to new technologies to keep afloat. Sure, the consequential ........
Read MoreIPMC GHANA

Stay Safe and Rlevant in Post Covid World
How technology keeps you relevant in post covid times. The global pandemic has impacted the behaviours of individuals, businesses, and institutions alike ........
Read MoreIPMC GHANA
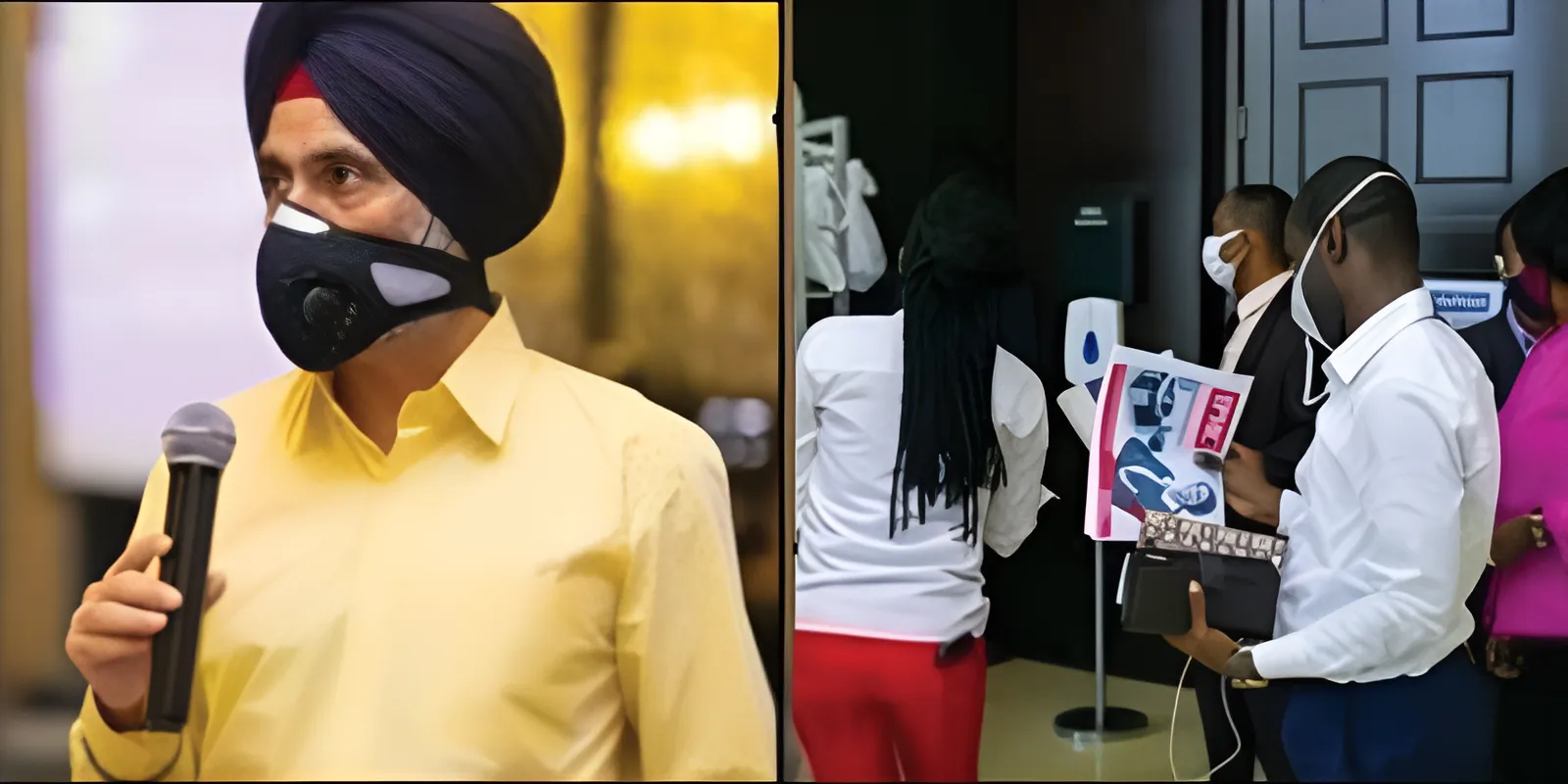
Progress in Times of Covid Seminar By IPMC and Dell With HDF SAS
IPMC Ghana & Dell in collaboration with @HDF Sas, successfully conducted a seminar on Data Protection at the Kempinski Gold Coast, Accra, on 24th June, 2020.
Read More IPMC GHANA
Door to Door Delivery of 5000 Onw-Month-Ration Boxes
Today was our first day of setting up a large scale packing & distribution center for the Government of Ghana and Private Sector Food Relief Program Partnership Project ........
Read MoreIPMC GHANA

IPMC Helps The Informal Sector During Covid-19 Lockdown
IPMC Ghana & Dell in collaboration with @HDF Sas, successfully conducted a seminar on Data Protection at the Kempinski Gold Coast, Accra, on 24th June, 2020 ........
Read MoreIPMC GHANA

IPMC Supports Food Victims of The Upper East Area of Ghana
Upon hearing the sad news of 20 persons losing their lives to floods on 17th oct 2019 in the upper east area of Ghana, IPMC immediately dispatched its team on 18th oct........
Read More IPMC GHANA
IPMC CEO At The Leadership 'Level Up' Conference In Kelowana, BC Canada
In his introductory speech for the famous author Darren Hardy, Mr. Amar Deep S. Hari expressed that similar to the human quality of love for a pet, universal in most humans ........
Read MoreIPMC GHANA

Helping Out When We Can, Where We Can AT IPMC
Upon hearing the sad news of 20 persons losing their lives to floods on 17th oct 2019 in the upper east area of Ghana, IPMC immediately dispatched its team on 18th oct ........
Read MoreIPMC GHANA

IPMC HP Security Event 2018
Information Technology (IT) companies IPMC and HP create new possibilities for technology to have a meaningful impact on business. The desire to always exceed expectations ........
Read More IPMC GHANA
IPMC Cisco Event
Ghana’s Top IT Company IPMC along with Cisco conducted a security seminar at Holiday Inn on Tuesday, 29th November 2016. The seminar saw huge attendance ........
Read MoreIPMC GHANA

IPMC Ghana Enters Strategic Partnership With Huawei Technologies
Ghana’s top IT firm, IPMC has signed a partnership agreement with China's leading Telecom conglomerate, Huawei Technologies. Under this strategic agreement, Huawei will use.......
Read MoreIPMC GHANA